251115_PwnSecCTF learning record
251115_PwnSecCTF learning record
cvestoneIn the full-stack CTF player program, this article will be continuously updated with recreated learning content
Attachments
Release 251115_PwnSecCTF · cvestone/cvestone.github.io · GitHub
EventInfo
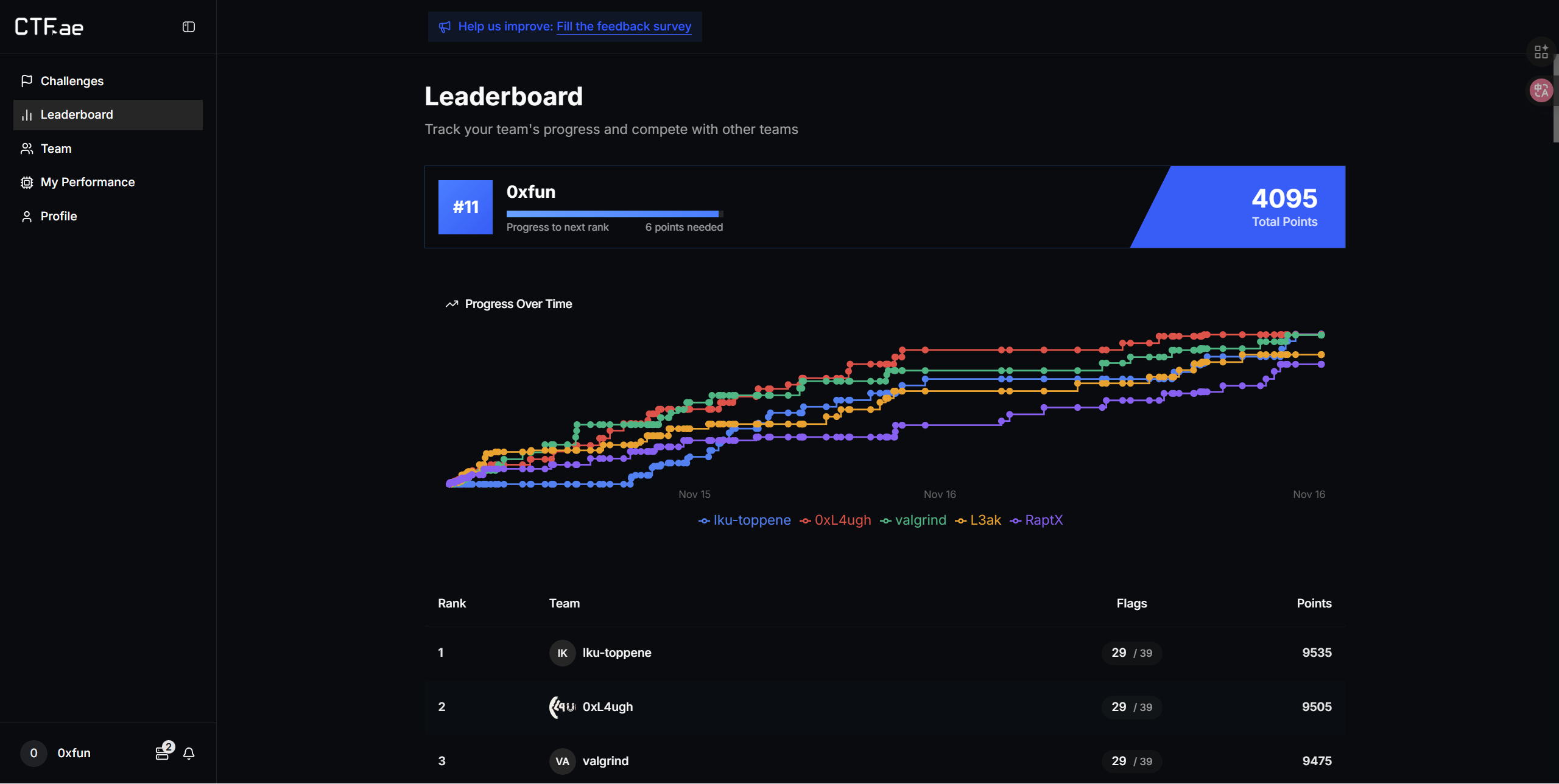
ScoreBoard
My team 0xfun’s rank in this event - top 11:
crypto
Opera
Desc
Writer was too lazy to write a description, so here’s this video: https://www.youtube.com/watch?v=lVlgMEFu1PI
- @solaire
Key Points:
CuteLwe
Desc
I Love TEA. Like, how can u hate TEA? TEAFTW
- @ibrahim
Key Points:
Orbital Permutations
Desc
In a land of mysteriously rotating thingies, orbits keep shifting and permutations keep permuting. Find the orbit jumps, solve the permutations, and uncover the flag!
- @supasuge
Key Points:
Wordler
Desc
I want to challenge you to a game of wordle, with a small twist…
- @lombard
Key Points:
Afraid Of Aelmo
Desc
Aelmo rules Cyberville from a mirrored palace where voices are logged and wiped. You, a silent cryptographer, hide a tiny, untraceable key inside the city’s boot, no grand revolt, just a whisper of code that reclaims the network one muted heartbeat at a time.
- @lombard
Key Points:
3AM
Desc
https://www.youtube.com/watch?v=FtutLA63Cp8
- @ibrahim
Key Points:
reverse
Malayo
Desc
Under the sound of the wild, The Malayopython appears
- w3rty
Key Points:
Hexllz
Desc
I think IDA forgot some architecture.
- @rayan
Key Points:
jump
Desc
I don’t know, i just need to jump
- @ryuk
hints:
- To defeat the obfuscation, you need to determine true/false opaque predicates and calculate the jmp value
- The program will utilize seccomp to validate your input
Key Points:
z3r0-day-project
Desc
Our Security Operations Center (SOC) has flagged a suspicious event. An employee reported receiving a seemingly benign Excel spreadsheet, and shortly after, our network intrusion detection system (IDS) logged unusual outbound traffic from their workstation. We fear this was a multi-stage attack culminating in data theft. We have successfully captured the full packet capture from the suspected timeframe and have also recovered the initial lure file. Your task is to perform a full analysis of these two artifacts. You must reconstruct the attack chain, uncover the attacker’s methodology, and ultimately determine what data was exfiltrated.
- Nyx
Key Points:
pwn
Pet-Management
Desc
A simple pet management program — have fun exploring it!
- kuvee
Key Points:
pwn-web-app
Desc
Is it web?
- @cmdking
Key Points:
my_note
Desc
I made the note program safe… I think.
- @daeseong
Key Points:
jǫklum-skógar/mǫrk
Desc
- the Mobile DEVKIT Unit was deployed as part of Rhine-Lab’s experimental command-control and communication suite for the Sami Expedition Initiative. using an ancient Android 7, it served as a field-grade testing platform for high-latency signal relays and environmental data synchronization.
following an unexpected blizzard and the emergence of a high-energy anomaly within the Sami perimeter, all outbound transmissions have ceased and the research team’s current status is unknown.
contained within the attachment are the full operational protocols and override access sequences for the DEVKIT.
— — — End of Transmission — — —
May Amma’s blessing guide your way, Dokutah~
Download:
https://master-platform-bucket.s3.us-east-1.amazonaws.com/challenge_resources/scien-document.zip
Mirrors (Choose one):
nc -v scien.pwnsec.team 1001
nc -v scien.pwnsec.team 1002
nc -v scien.pwnsec.team 1003
nc -v scien.pwnsec.team 1004
nc -v scien.pwnsec.team 1005
- @muwa
Key Points:
misc
PyJail
Desc
Python sandbox challenge, Can you escape the jail?
- @Muhammed
Key Points:
MQTT_Traffic
Desc
MQTT is widely used in IoT because it is lightweight and works well on devices with low power, low bandwidth, and limited resources. This capture shows MQTT over TLS from a legacy gateway. The security team has identified that the TLS handshake uses an RSA key exchange. Can you recover the plaintext?
- @hiddenenv
Key Points:
Lucid Dream
Desc
I had a weird dream. Couldn’t make sense of it. Woke up and found this file under my pillow.
The data felt incomplete and encoded in multiple ways. If I could clean it up and learn from the patterns, perhaps the dream would reveal its meaning.
‘oh’ is an acronym. Also, c8 is missing. Coincidence? Also, I vividly remember the dream’s charset being ^[a-z0-9{}_]$
- @habema
hints:
‘oh’ is an acronym. Also, c8 is missing. Coincidence? Also, I vividly remember the dream’s charset being ^[a-z0-9{}_]$
Key Points:
Guarding The Rails
Desc
The tripwires are set. The guardrails are up. Don’t make a wrong move, or the alarm will sound.
- @habema
Key Points:
Babyjail()
Desc
Python Jail() .
- @Muhammed
Key Points:
PyDocs
Desc
A tiny terminal document manager powers an overconfident admin’s workflow.
- @Muhammed
Key Points:
forensics
Desc
Just chatting
https://master-platform-bucket.s3.us-east-1.amazonaws.com/challenge_resources/HiddenData.zip
- @Abdullah
Key Points:
Sherlock
Desc
Our systems were compromised by a recent internal attack. Fortunately, our IT admin managed to get a network capture before the attacker deleted all his traces. Please perform a DFIR investigation to uncover what actually happened. Note: The flag is split into 3 parts: - Part one: What is the username of the first compromised user? - Part two: What is the final compromised user’s NTLM hash? - Part three: You have to get this last part on your own. This part contains the } wrapper of the flag. Flag format: flag{username_NTLNHash_lastPartOfTheFlag} (submit the first two parts in lowercase).
- @kujen
Key Points:
The Hound
Desc
Kuvee, our intern, got hacked as usual. Please answer the following questions to try and figure out what happened so kuvee doesn’t fall for it again!
https://netorgft15219885-my.sharepoint.com/:u:/g/personal/fsaidi_intrinsic_security/ET9AnRYWEqtHvvmLqZd5WuQBCb0zpomEUqDmaqiyZJyMTA?e=RN0Ffc
- @kujen
Hints:
- cat /usr/share/wordlists/rockyou.txt| head -650000 | tail -25000
- the attack was a zero click attack. Means it required no user interactions of the target user. And would also require the attacker to have access to a shared directory with the target. Hope this helps.
- Take a look at CVE-2025-50154, don’t get too deep in it but understand it. And pay close attention to the file extension used in it. An attacker would deliver it in a shared folder under C:/. Also the group name is DEVTEAM and the password is ‘!jerlynn.c!1’ . Solve it!
Key Points:
mobile
CuteFrida
Desc
This app is so cute yet so susy, isn’t it?
- @TK
Key Points:
RudeFrida
Desc
Say hello to RudeFrida, it is like your toxic ex who gaslighted you for loving her.
- @TK
Key Points:
FreakyFrida
Desc
It started as just another night at the lab. You opened Android Studio, loaded an APK, and whispered those famous words: “Let’s hook something simple…” Frida purred in the terminal. Everything seemed fine — until it wasn’t. Your screen flickered. Logcat went wild. The app whispered back. “Nice try, human.” Suddenly, “console.log(flag)” returned nothing. MainActivity crashed like your hopes of passing OSCP on the first try. You tried again, but the app laughed — a distorted sound echoing through JNI hell. “You think you can control me?” it taunted. Frida was no longer your tool; it had become the master. The app morphed, adapting to your every move. To retrieve the flag, you must outsmart the app’s new defenses. Can you break free from Frida’s grip and reclaim control? Note: they told me to use a Frida version lower than 17, and I totally agree with that advice, you should too.
- @TK
Key Points:
web
warmup(√)
Desc
Just a normal warmup challenge
here is the guest creds guest:guest123
the flag is in /flag.txt
- @qlashx
Key Points: IDOR、SSRF bypass
OhMyPP
Desc
simple web aPP 🧢
- @x6vrn
Key Points:
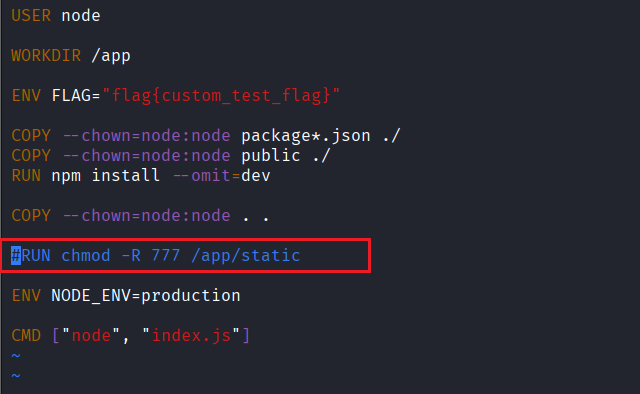
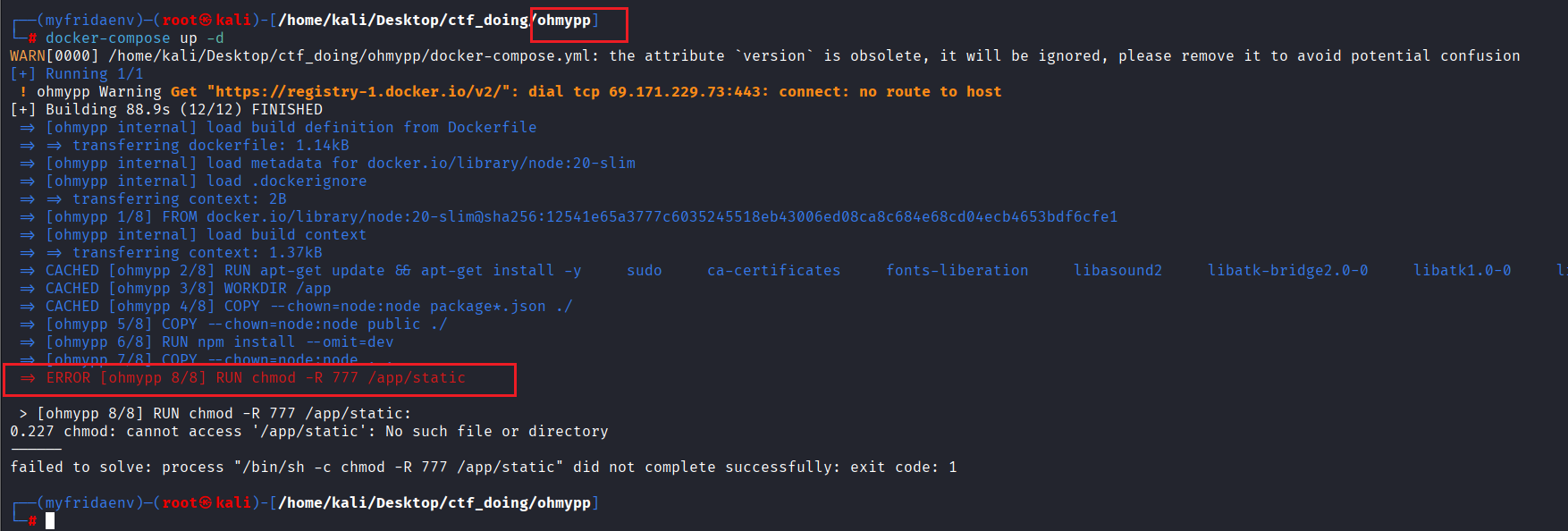
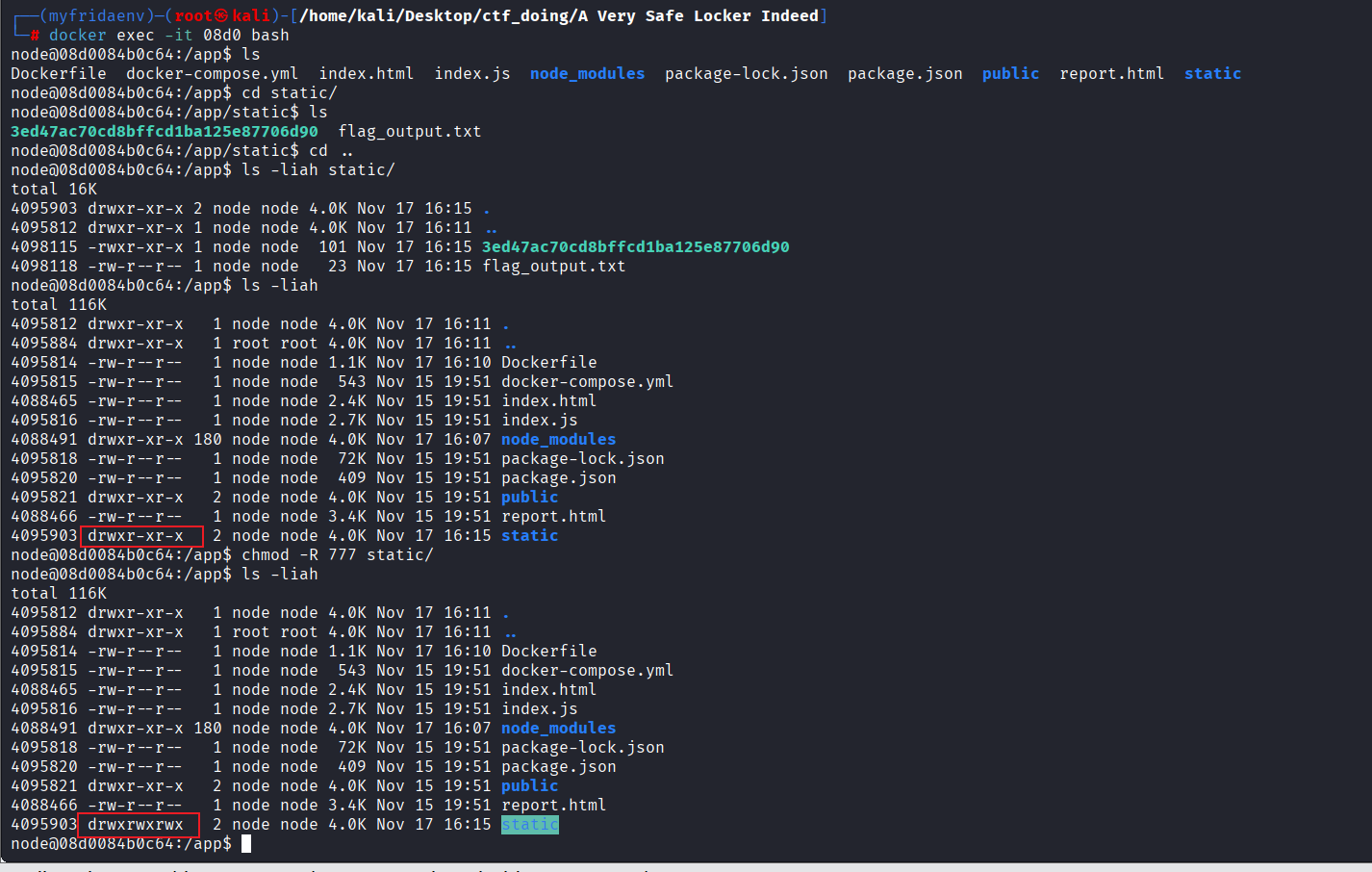
Notice:if want to deploy locally, need to ignore this static in Dockerfile:
or it will be failed like this:
Then manually configure it to ensure the original challenge settings are preserved:
1 | #!/usr/bin/env python3 |
FireLeak
Desc
Leaking with fire is it enough?
- @x6vrn
Key Points:
A Very Safe Locker Indeed
Desc
We upped our security since last year, and now our lockers are more exclusive than ever! The only thing we couldn’t quite work around is the master’s authority, can you get yourself a locker and trick him into giving you the secret flag?
- @moha09
Key Points:
A Very Safe Locker For Real Now
Desc
We upped our security since last year, and now our lockers are more exclusive than ever! The only thing we couldn’t quite work around is the master’s authority, can you get yourself a locker and trick him into giving you the secret flag? We have patched the unintended. Find the vulnerable source code from ‘A Very Safe Locker Indeed’ (with the unintended). Show me how you solve it now.
- @moha09
Key Points:
PSPD
Desc
They begged me not to do it, but I had to. Can you bring PwnSec’s Police Department to a clojure?
- @aelmo
Key Points:
MaxPayne
Desc
Not everything ages like fine wine.
- @Logan0x
Key Points:
MaxPayne Revenge
Desc
Not everything ages like fine wine. I mean it this time.
Download source code for previous challenge, “MaxPayne”. It does not affect the intended solve.
- @Logan0x
Key Points:
cloud
Pizza Hub
Desc
our genz intern built a cloud-based pizza-delivery app for our team, however our SOC reported that his account credentials were briefly exposed! Link: http://pizzahub.pwnsec.team/index.html Note: Fuzzing is strictly forbidden; it will not help you.
- @chxmxii
Key Points:
The Fall of the Great Wall
Desc
Can you pass the Great Wall’s defenses and retrieve the hidden artifact? https://greatwall.blob.core.windows.net/
- @CodeBreaker
Key Points:
fortress of solitude
Desc
Welcome to the sky version of the fortress of solitude, its heavily weaponized and not easily accessible. https://dokvw9cgkho3i.cloudfront.net/
- @CodeBreaker