240705_downunderCTF learning record
240705_downunderCTF learning record
cvestoneIn the full-stack CTF player program, this article will be continuously updated with recreated learning content
Attachments
Release 240705_DownUnderCTF · cvestone/cvestone.github.io · GitHub
EventInfo
crypto
xxx
Desc
Key Points:
reverse
adorable encrypted animal
Desc
An adorable animal was encrypted with this program! A flag too, I guess.
NOTE: aea and libAppleArchive.dylib are provided for your convenience. They are taken without modification from the macOS system that ran the binary.
Author: joseph
Key Points:
average assembly assignment
Desc
This is just your average assembly assignment.
Author: joseph
Key Points:
dungeon
Desc
You find yourself in a strangely orderly dungeon, with doors in each cardinal direction, some locked, some unlocked. At any rate, it seems dangerous and you likely want to find a way out.
SSH password: ductf
Author: joseph
Key Points:
jmp flag
Desc
The flag is just a hop, a skip and a jump away.
Author: joseph
Key Points:
Desc
If you think about it, a lot about solving CTFs is pressing the right buttons in the right order. So we made an app to help you practice that.
Author: joseph
Key Points:
rusty vault
Desc
I’ve learnt all the secure coding practices. I only use memory safe languages and military grade encryption. Surely, you can’t break into my vault.
Author: 1nval1d (Cybears)
Key Points:
Ternary Brained
Desc
We received a coded message from a parallel version of New Zealand. We also have a copy of the encoder they used to make the message.
Author: @jscarsbrook and @pix
Key Points:
pwn
sign in
Desc
Please sign in as root to get a shell.
Author: joseph
Key Points:
sheep farm simulator
Desc
Practice your sheep grooming skills with this sheep farm simulator!
Author: joseph
Key Points:
pac shell
Desc
Welcome to pac shell v0.0.1. You have arbitrary read and write, please turn this into arbitrary code execution!
Author: joseph
Key Points:
mirage
Desc
A classic v8 challenge - pwn the renderer to steal the flag!
Author: grub and anvbis
Key Points:
Faulty Kernel
Desc
Keep your valuable data safe in a shared buffer!
Author: toasterpwn
Key Points:
ESPecially secure boot
Desc
Tags: hardware
The ESP-IDF 2nd stage Bootloader implements functions related to the Secure Boot feature. In previous releases of ESP-IDF releases (2.x, 3.0.5, 3.1), the 2nd stage Bootloader did not sufficiently verify the load address of binary image sections. If the Secure Boot feature was used without the Flash Encryption feature enabled, an attacker could craft a binary which would overwrite parts of the 2nd stage Bootloader’s code whilst the binary file is being loaded. Such a binary could be used to execute arbitrary code, thus bypassing the Secure Boot check.
Author: joseph, HexF
Key Points:
hardware
Birdloader
Desc
The kiwis can’t turn on their device anymore. Maybe you can get it to work?
We have connected your RP2040 to what appears to be a 9600baud serial port. You TX (device RXes) on pin 8; you RX (device TXes) on pin 9.
Author: HexF, Jamie
Key Points:
Crash Landing
Desc
Tags: rev
Our little kiwi is trying to fly!
Author: HexF
Key Points:
DUCTF
Desc
Tags: crypto
DownUnder Cabs, Trains & Ferries have an interesting pre-pay card system. Maybe its vulnerable to something?
NOTE: There was a slight mistake connecting the SPI lines correctly, requiring you to bit-bang SPI instead. A bitbang SPI implementation has been provided for you.
Author: HexF
Key Points:
I See
Desc
I too see the kiwi and the emu over there!
We suggest you solve this challenge before attempting any others.
Author: HexF
Key Points:
sirkit
Desc
We intercepted some design files. Maybe you can make sense of them?
Author: HexF
Key Points:
Sounds Nice
Desc
Tags: osint
I’m trying to reverse engineer this sound bar. Maybe you can answer my questions about this?
- Which bluetooth chipset is used?
- What is wireless audio chipset used?
- What is the value of the coupling capacitor, connected to the audio module’s RX antenna? Give your answer in pico-farads
- What is the pin number on the wireless audio chipset for the I2C clock signal?
Flag format: DUCTF{[1]_[2]_[3]_[4]}, all capitals.
Author: HexF
Key Points:
The Door
Desc
I lost the remote to the plane hanger door. Help kiwi get back in the air!
NOTE: Your code has a 5 minute runtime limit
Author: HexF
Key Points:
misc
xxx
Desc
Key Points:
steganography
xxx
Desc
Key Points:
forensics
Baby’s First Forensics
Desc
They’ve been trying to breach our infrastructure all morning! They’re trying to get more info on our covert kangaroos! We need your help, we’ve captured some traffic of them attacking us, can you tell us what tool they were using and its version?
NOTE: Wrap your answer in the DUCTF{}, e.g. DUCTF{nmap_7.25}
Author: Pix
Key Points:
Bad Policies
Desc
Looks like the attacker managed to access the rebels Domain Controller.
Can you figure out how they got access after pulling these artifacts from one of our Outpost machines?
Author: TurboPenguin
Key Points:
emuc2
Desc
As all good nation states, we have our own malware and C2 for offensive operations. But someone has got the source code and is using it against us! Here’s a capture of traffic we found on one of our laptops…
Author: BootlegSorcery@
Key Points:
Lost in Memory
Desc
Looks like one of our Emu soldiers ran something on an Outpost machine and now it’s doing strange things. We took a memory dump as a precaution. Can you tell us whats going on?
This challenge has four parts to combine into the final flag with _ between each answer. Find all four answers and combine them into the flag as all lower case like DUCTF{answer1_answer2_answer3_answer4} eg. DUCTF{malicious.xlsm_invoke-mimikatz_malware.exe-malware2.exe_strong-password123}
- What was the name of the malicious executable? eg
malicious.xlsm - What was the name of the powershell module used? eg
invoke-mimikatz - What were the names of the two files executed from the malicious executable (In alphabetical order with - in between and no spaces)? eg
malware.exe-malware2.exe - What was the password of the new account created through powershell? eg
strong-password123
Author: TurboPenguin
Key Points:
Macro Magic
Desc
We managed to pull this excel spreadsheet artifact from one of our Outpost machines. Its got something sus happening under the hood. After opening we found and captured some suspicious traffic on our network. Can you find out what this traffic is and find the flag!
Author: TurboPenguin & Pix
Key Points:
SAM I AM
Desc
The attacker managed to gain Domain Admin on our rebels Domain Controller! Looks like they managed to log on with an account using WMI and dumped some files.
Can you reproduce how they got the Administrator’s Password with the artifacts provided?
Place the Administrator Account’s Password in DUCTF{}, e.g. DUCTF{password123!}
Author: TurboPenguin
Key Points:
osint
xxx
Desc
Key Points:
web
co2
🚩wait
Desc
A group of students who don’t like to do things the “conventional” way decided to come up with a CyberSecurity Blog post. You’ve been hired to perform an in-depth whitebox test on their web application.
Author: n00b.master.
Key Points:
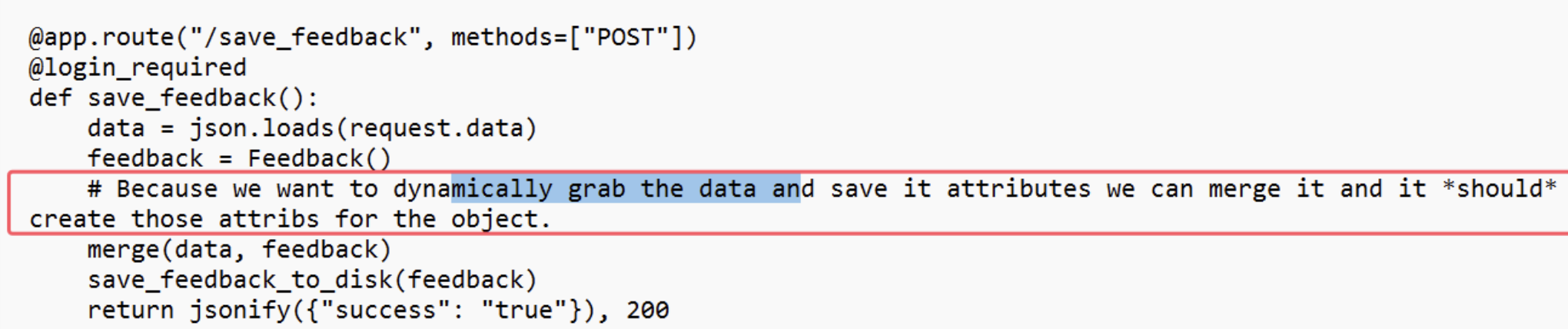
Identify that it is a Flask framework. During the audit, in app/routes.py, which is the route configuration file, there appears to be a seemingly important comment:
However, unfortunately, it ultimately could not be successfully interpreted. I don’t know how to utilize this key information next.
Notice the note:
1 | Because we want to dynamically grab the data and save it attributes we can merge it and it *should* create those attribs for the object. |
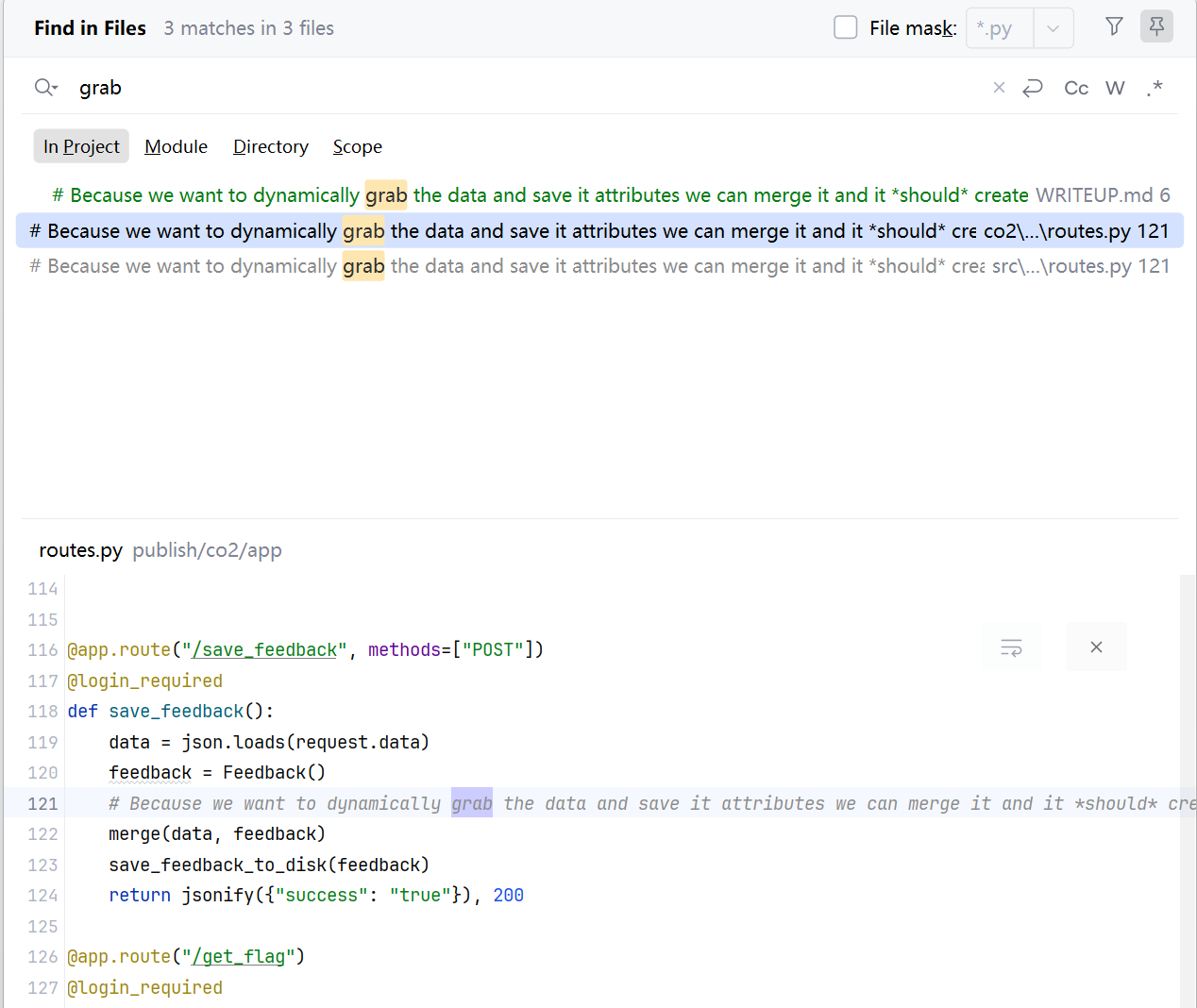
After reading the official writeup, this part of the comment is indeed the entry point. The writeup gave me an idea: we can extract all the particularly distinctive and crucial verbs from the comment, then perform a global search for these verbs. This might allow us to gather more information:
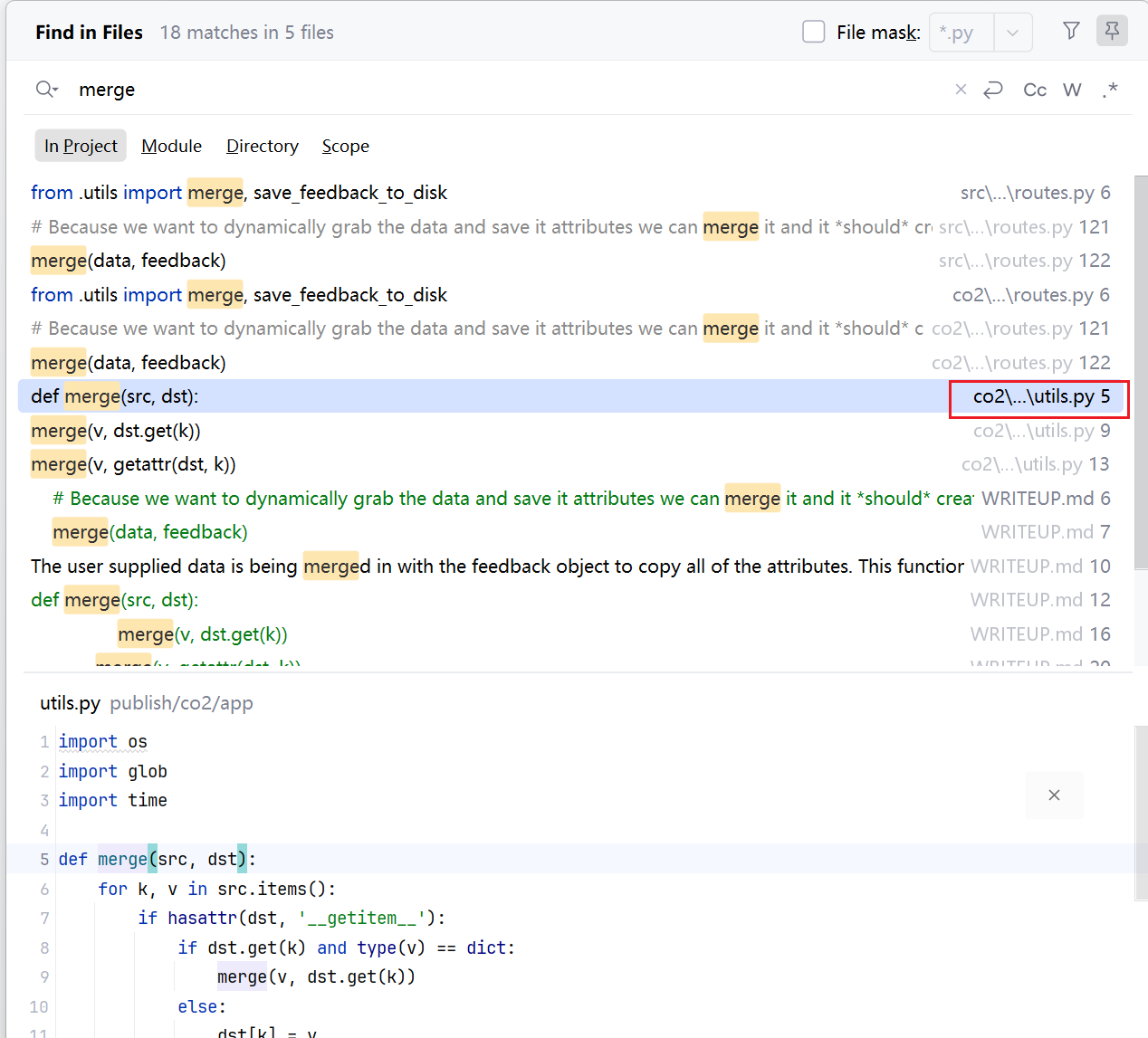
Only one utils.py was found. Let’s take a look inside:
From the reference article provided by the official source, I learned that this challenge actually deals with Python “prototype” pollution, more accurately referred to as class pollution, since the concept of a prototype doesn’t exist in Python; that concept originates from JavaScript. However, Python’s built-in attributes are very similar to prototypes.
Before understanding Python’s class pollution, let’s first look at JavaScript’s prototype pollution, as the former is an extension and analogy of the latter.
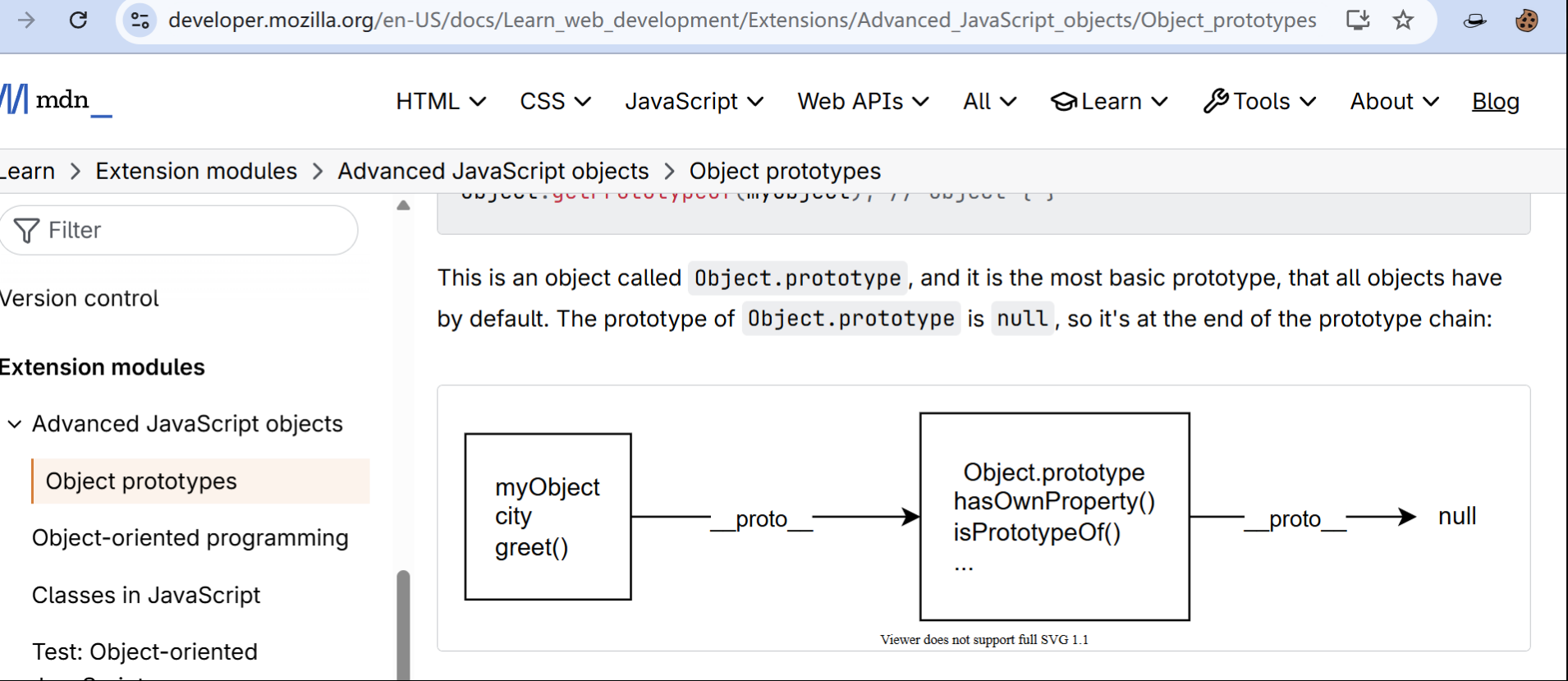
First, what is a prototype?
A prototype is a built-in property of every object in JavaScript. It is itself an object, so a prototype also has its own prototype, forming what is known as the prototype chain. This sounds very similar to inheritance in other object-oriented languages. You can think of the prototype as the “parent” of an object, containing certain properties and methods. When you create a new object, JavaScript automatically links this object to its parent prototype. This means the new object can inherit properties and methods from the parent prototype. The benefit of using prototypes and the prototype chain is that we can share properties and methods between objects, avoiding the need to repeatedly define the same code.
For more knowledge about JavaScript prototypes, refer to this document.
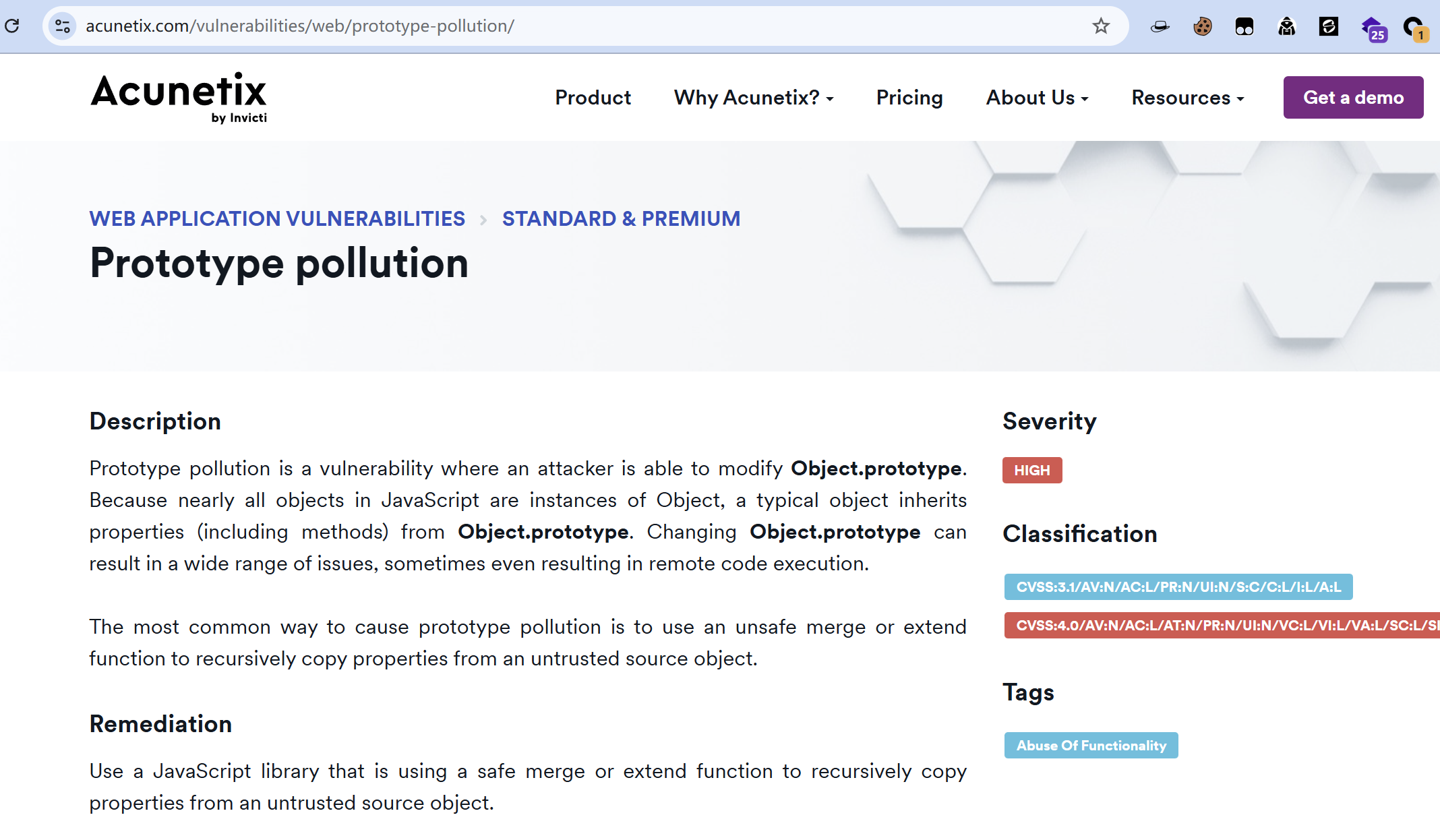
So, what is prototype pollution then?
We should also know some about Object.prototype:Object is a built-in constructor function used to create objects. Object.prototype is the prototype of the Object constructor, providing common properties and methods that can be inherited and accessed by other objects. Object.prototype sits at the top of the prototype chain and is the root prototype shared by all objects. When we create a new object, this object is automatically linked to Object.prototype, forming the prototype chain. Through the prototype chain, objects can inherit and access the properties and methods defined on Object.prototype.
Note: Although
Object.prototypeis the root prototype, not all objects directly inherit from it. In fact, each object has its own prototype, which can be another object specified via the constructor’s prototype property.
Understanding this, it seems more and more like there isn’t a huge difference from Java’s class inheritance. So why did JavaScript specifically introduce this unique concept of prototype?
Analyzing from the perspective of language characteristics and application requirements, I realized: because JavaScript is a dynamic, interpreted scripting language, while Java is a static, compiled language. JavaScript was originally designed for web programming, requiring extensive dynamic interaction on the client side. Prototypal inheritance allows objects to dynamically inherit and modify properties and methods at runtime, without needing a fully defined inheritance relationship at compile time. Furthermore, almost all data in JavaScript are objects, so prototypal inheritance fits JavaScript’s object model more naturally, representing relationships between objects more intuitively. Additionally, the syntax of prototypal inheritance is relatively concise. Unlike classical inheritance, there’s no need to define classes and subclasses. In JavaScript, we can achieve inheritance directly by creating objects and setting prototypes, without introducing extra syntax and concepts.
In contrast, inheritance in Java is based on classes and interfaces. It involves creating subclasses to inherit the properties and methods of a parent class. The inheritance relationship must be determined at compile time and remains static within the class hierarchy. This means that in Java, the class inheritance relationships are defined at compile time and cannot be dynamically modified at runtime, including the relationships themselves or the properties and methods.
In summary, JavaScript is more flexible and dynamic, whereas Java focuses more on reliability, security, and performance, prioritizing stability.
Therefore, when we “pollute” (or tamper with) the
Object.prototype, according to the inheritance mechanism and its position, all prototypes on this chain and the objects associated with these prototypes will be affected. They will dynamically inherit the “polluted” properties and methods from the prototype at runtime. This is a disaster with an extremely wide scope of impact.
Returning to the study of our main focus this time – “class pollution” in Python:
After reproducing the examples from the official reference article, I have gained a basic understanding of class pollution.
co2v2
Desc
Well the last time they made a big mistake with the flag endpoint, now we don’t even have it anymore. It’s time for a second pentest for some new functionality they have been working on.
Author: n00b.master.
Key Points:
i am confusion
Desc
The evil hex bug has taken over our administrative interface of our application. It seems that the secret we used to protect our authentication was very easy to guess. We need to get it back!
Author: richighimi.
Key Points:
sniffy
Desc
Visit our sanctuary to hear the sounds of the Kookaburras!
Author: hashkitten.
Key Points:
hah got em
Desc
Deez nutz
Hah got em
…
Oh by the way I love using my new microservice parsing these arrest reports to PDF
The evil bot (2024)
Author: ghostccamm.
Key Points:
waifu
Desc
The big bad bot got a bit lonely after a hard day of work and made a Web Artificial Intelligence Firewall Utiliy (WAIFU) to talk with and block hacking attempts.
Can you bypass the bot’s WAIFU?
Important Note:
Use 127.0.0.1 (not localhost) instead of container names (the ports the services are listening on are the same).
Author: ghostccamm.
Key Points:
Prisoner Processor
Desc
The bug had a microservice for conveting JSON to YAML to assist with processing prisoners it has captured.
Can you try to find a way to hack this microservice so we can get an initial foothold into the bug’s prison system?
Author: ghostccamm.